Taking Risks?
Not with your OT-Security
Taking Risks?
Not with your OT-Security
Taking Risks?
Not with your
OT-Security
Business-Driven OT Cybersecurity
OT Cybersecurity has matured. Yesterday’s focus on vulnerability mapping and passive threat detection has made way for a higher level of proactive protection, incorporating continuous risk management and total visibility into all device properties and inter-device attack vectors.
This transformation allows CISOs and industrial operators to improve network resilience while optimizing the OT security system based on preferences and budgetary constraints.
We invite you to demo Radiflow’s OT-security platform and how it can significantly reduce your exposure to network risk while increasing the ROI of your Cybersecurity operation.
New version of CIARA offers non-intrusive Breach & Attack Simulations
Digital image-based simulations, using thousands of data points for network, asset & attack tactics, account for criticality of business processes to improve the optimization of ROI expenditure.
ROI-driven industrial threat detection & risk management solutions
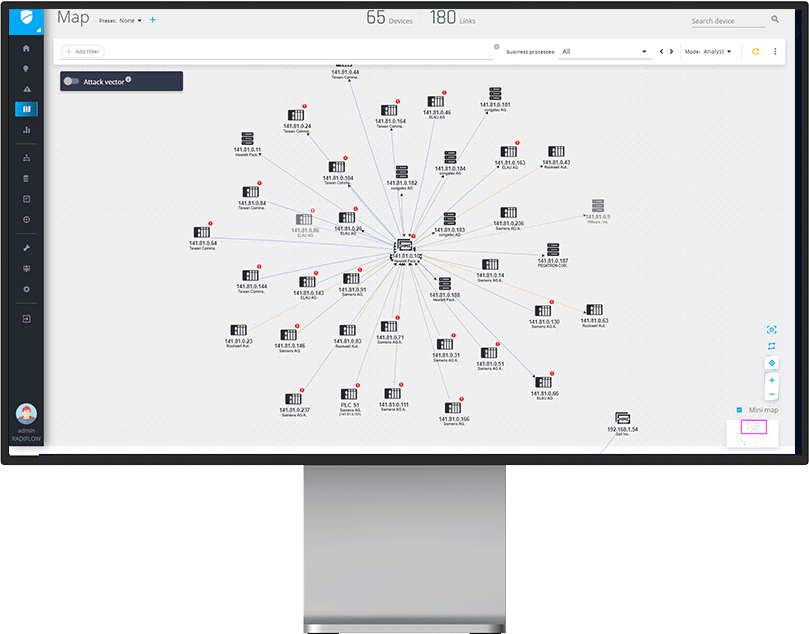
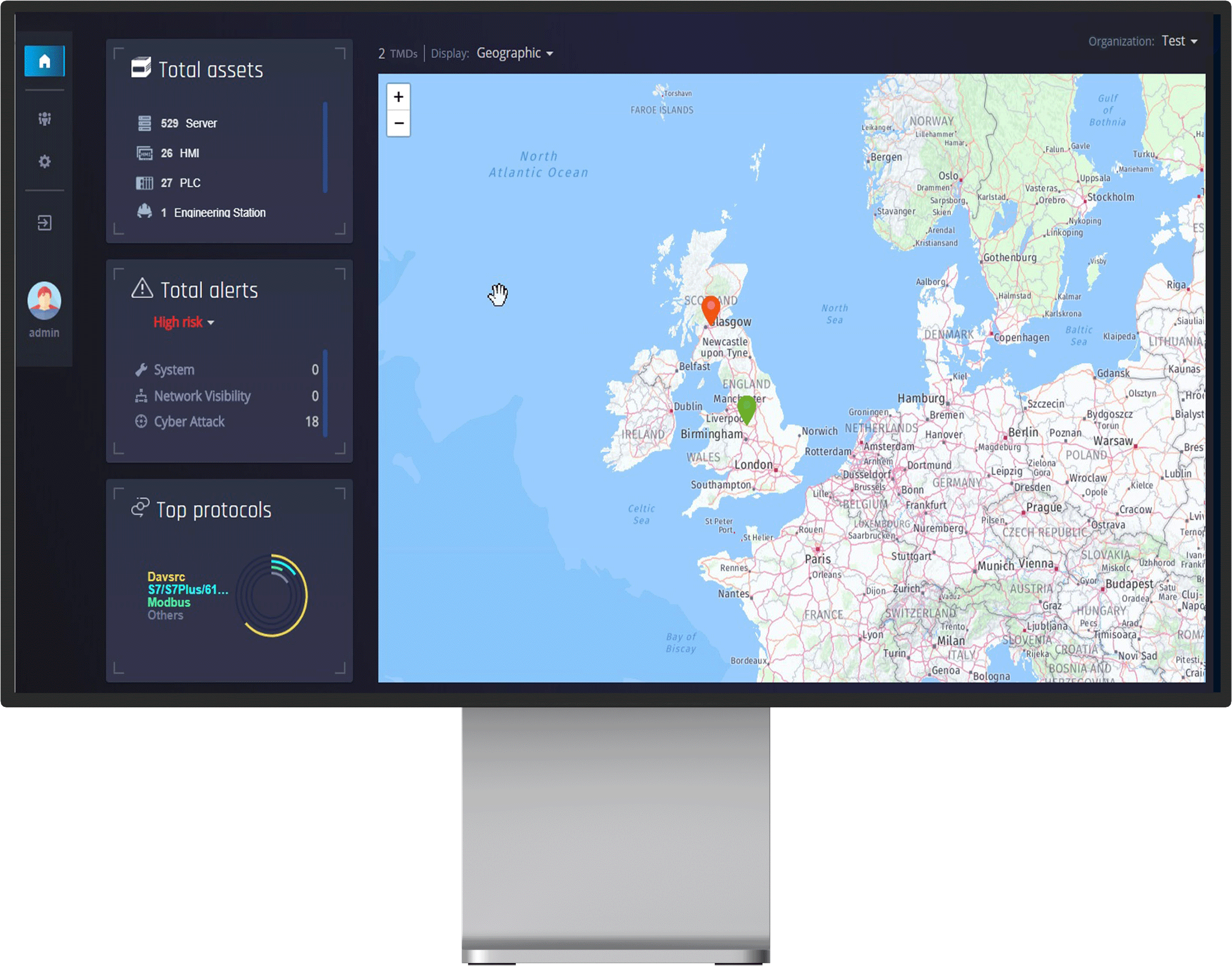
Digital Imaging & Network Visualization
- Non-intrusive construction of network digital image
- Complete network map, down-drillable to all device & vulnerabilities
- Attack-vector analysis for inter-process vulnerabilities
- WAN/LAN-friendly data transfer from remote facilities to central location using the iSAP smart collector
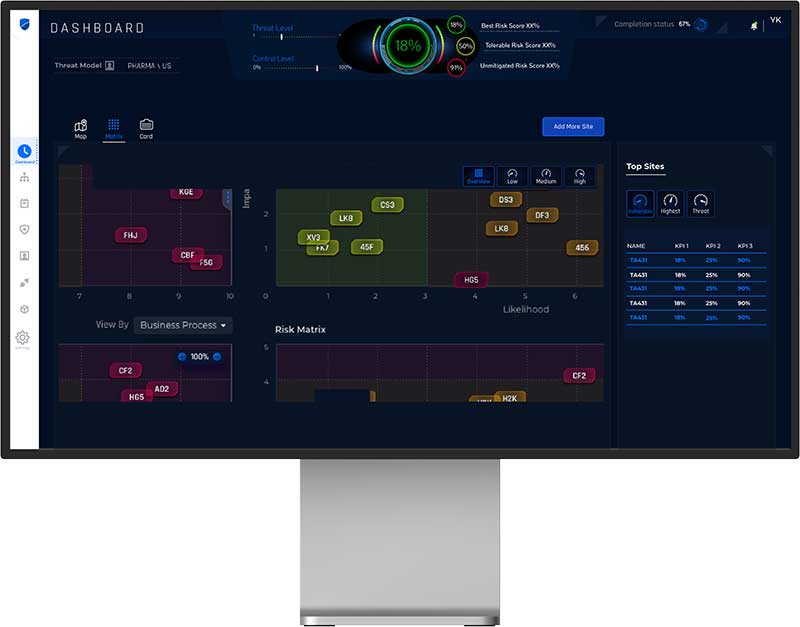
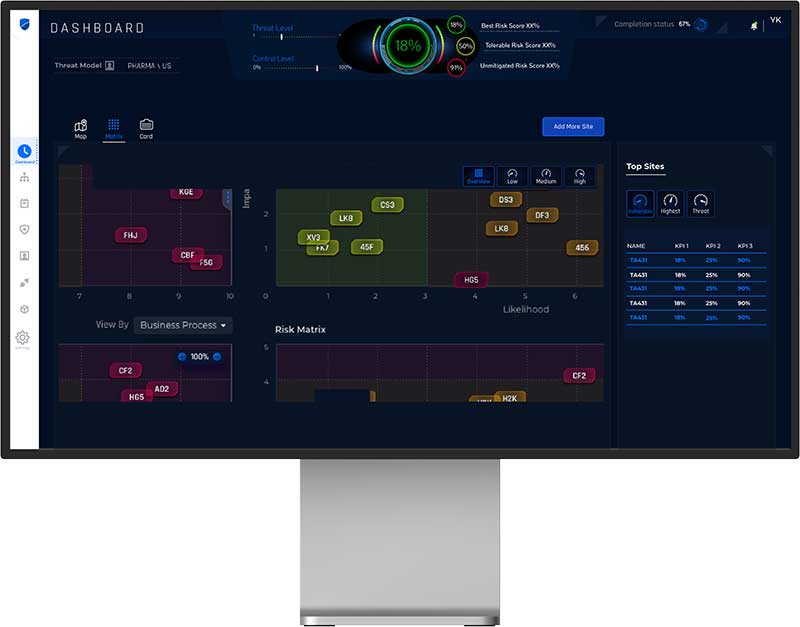
Risk Posture & Network Characteristics
- Non-Intrusive Breach & Attack Simulations (BAS) using MITRE ATT&CK and other TI sources
- Coverage of all IEC 62443 FRs + Supply Chain attacks
- Key indicators for Risk, Mitigation Control and Threat Levels
- Customizable reports for planning and auditing
Ongoing hardening & ROI optimization
- Alerting rules & device communication policies
- ROI-optimized mitigation plan based on preferences & budget
- Plain-language mitigation insights for ongoing network hardening
- DPI Secure Gateway/Firewall with work order-based remote access management
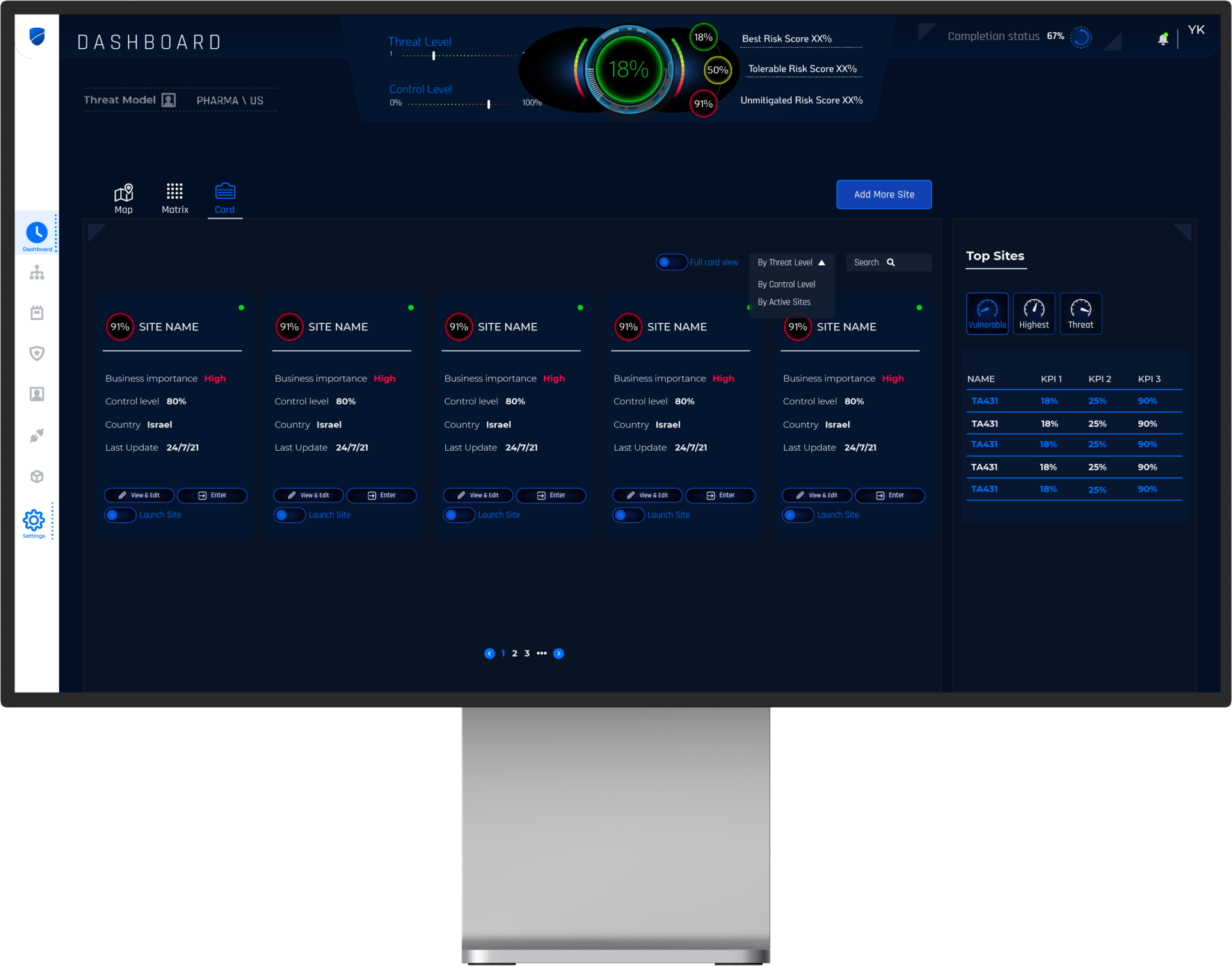
MSSP-Friendly Threat & Risk Monitoring
- Single-pane central management of multiple user’s iSID arrays
- Designed for corporate or MSSP’s SOC
- Configurable, customized alerts on anomalies and threats
- Continuous assessment of network risk posture
Dokumentation und Ressourcen
Radiflow by Numbers
Protected Sites
Customers Worldwide
Branchen
Stromerzeugung
Energieübertragung und -verteilung
Erneuerbare Energie
Wasser & Abwasser
Verkehrsmittel
Öl- und Gasförderung
Herstellung
Gebäudeleittechnik (GLT)
Subscribe to the Radiflow Security Newsletter
Radiflow’s monthly newsletter features industry and technology news related to the state of ICS/SCADA security, as well as new offerings and news from Radiflow.
