The Radiflow Security Blog
New Features in CIARA v1.3
CIARA is Radiflow’s ROI-driven, ISA/IEC 62443-compliant risk assessment & management platform. Since its introduction, it has earned industry-wide acclaim for its ability to non-intrusively simulate cyberattacks in industrial automation networks and prioritize the most effective mitigation measures for those threats, and provide the user with a structured plan for optimized OT security expenditure.
The release of CIARA v1.3 introduces a host of new features including flexible security optimization, new threat types, budget planning and integration with 3rd-party ICS security and management systems.
Here are just a few of the new features in CIARA v1.3:
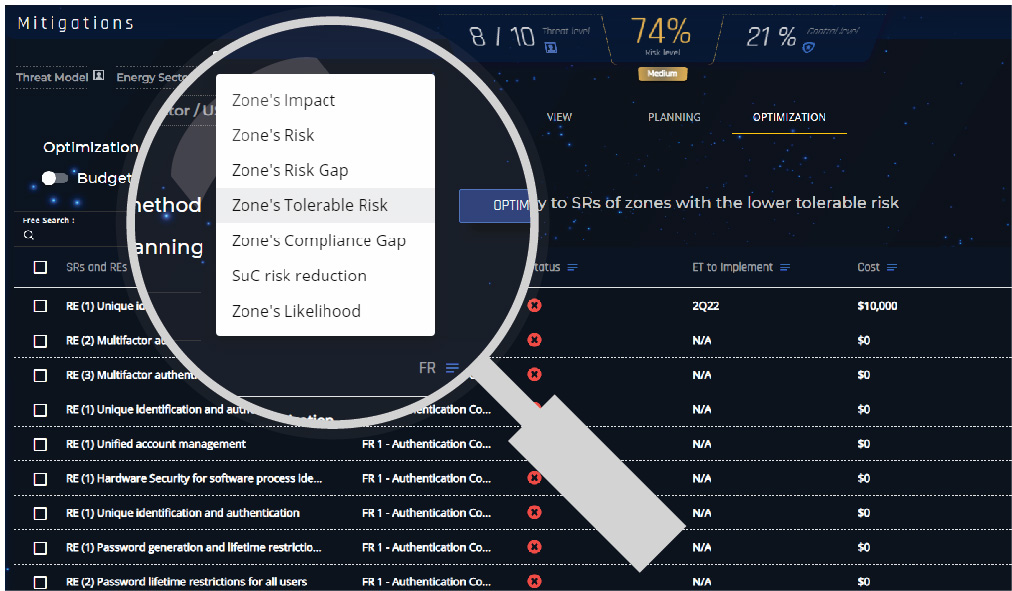
Set your own criterion for optimization
Users can now select between different risk-reduction criteria, that go beyond simply reducing network-wide risk.
The new criteria help users balance between long-term security needs (e.g. overall risk reduction) and short term needs (e.g. bring the network up to full compliance with the IEC 62443 standard.)
For each criterion CIARA will prioritize the SRs (security requirements for mitigation measures, e.g. “Authentication Control) related to specific Zones (distinctive business units as defined in IEC 62443, e.g. “Power Generation”) that match the criterion.
CIARA v1.3 optimization criteria include:
- Overall risk reduction
- Zone impact: Zone’s criticality, as defined by the impact (quantified in monetary terms) by a disabling cyberattack on that Zone
- Zone Risk: Zones with the highest risk score
- Tolerable risk: Zones with the lowest tolerable risk (as defined by the user)
- Risk gap: Zones with the highest discrepancy between tolerable risk and actual risk
- Compliance gap: Zones with the highest discrepancy between actual security measures and those prescribed in the IEC62443 standard
- Likelihood of attack: Zones most likely to be attacked
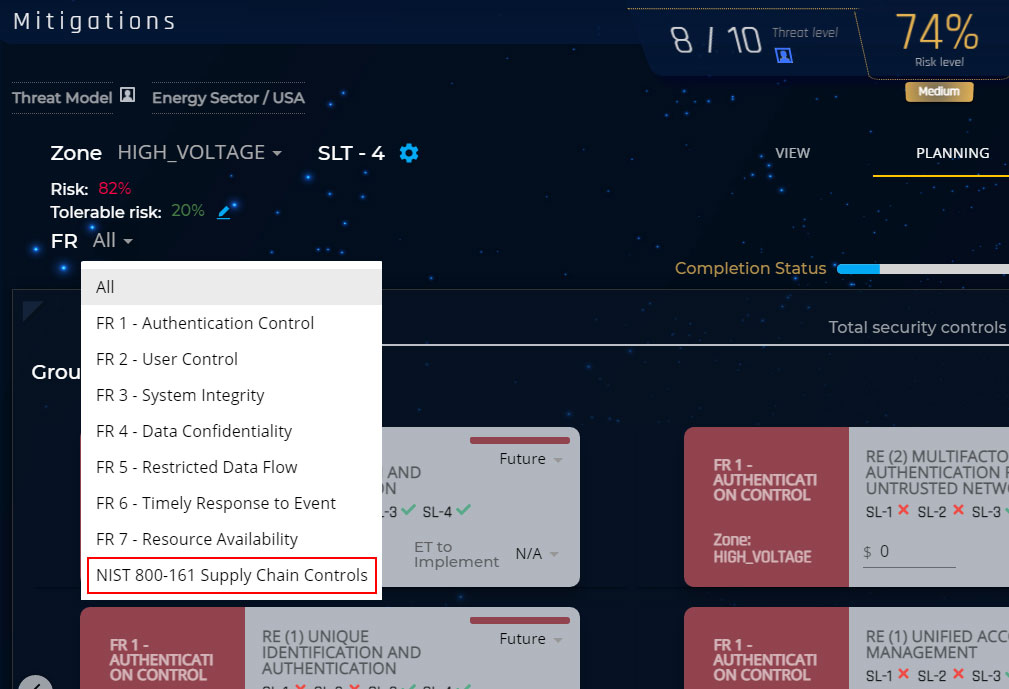
Added Control Group for Supply Chain attacks
Supply chain attacks, which are on the rise (as in the case of the SolarWinds attack), target organizations across all industries using vulnerabilities in their vendors’ networks, by means of adding a malicious payload to to vendors’ devices’ communications.
CIARA v1.3 adds a security control group for the NIST 800-161: Supply Chain Controls (in addition to the seven security control groups referring to the Fundamental Requirements (FRs) in IEC 62443.
This practical advantage to the user is that now supply chain attackers and tactics, as well as corresponding mitigations, can be included in CIARA’s breach & attack simulations (BAS) and in the subsequent optimized mitigation plan.
CIARA 1.3 introduces a new control group for supply chain attacks.
Quarterly Budget Planning
CIARA has been added an engine for budget planning, by quarter.
Once the user has entered estimated costs for mitigating various security requirements (SRs) and the organization’s quarterly OT security budget, CIARA will automatically generate a risk-mitigation plan, based on the user’s optimization preferences, that meets the user’s quarterly budget constraints.
The new budget planner in CIARA 1.3 generates a quarterly OT security plan for prioritized mitigations based on the user’s quarterly budget.
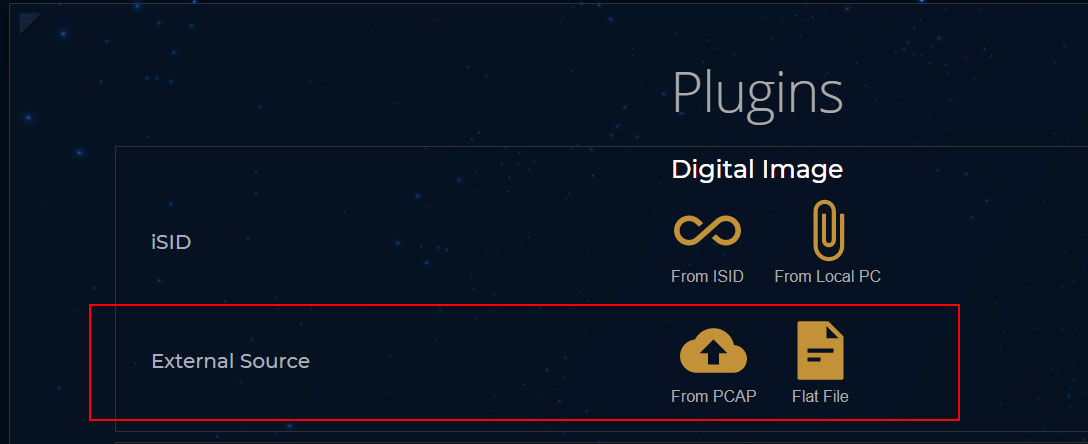
Analysis of 3rd-party network digital images
To eliminate the risk of running intrusive attack simulations on the live production network (which often include injection of actual malware), CIARA uses digital images of the production network for its risk analysis and OT BAS simulations.
Now CIARA is able to use digital images generated by a 3rd-party network modeling software. This allows users to leverage their existing investment in OT security technology.
CIARA v1.3 users can now upload a digital network image generated by a 3rd party system for risk analysis and optimization